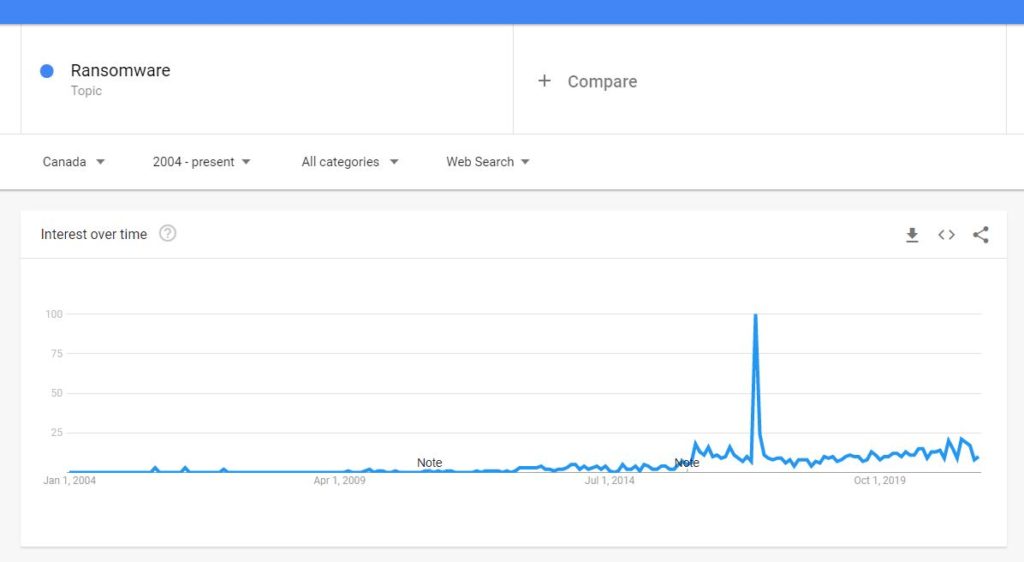
In the last decade or so, ransomware has frequently been in the news. Due to several high-profile attacks, it is a cyber threat that has found its way into the popular consciousness. This was especially true in 2017 when the infamous WannaCry attack hit. At its height, WannaCry infected more than 230,000 computers around the globe. This significantly affected many organizations, including the UK’s National Health Service (NHS). It also hit Honda, FedEx, Telefónica (a Spanish telecommunications firm headquartered in Madrid) and many others.
You may also remember the Colonial Pipeline cyberattack from the spring of 2021. That attack affected some of the equipment managing the pipeline. The pipeline carries up to three million barrels per day between New York and Texas, delivering gasoline and jet fuel to the Southeastern US. The attack led to the pipeline operator, Colonial Pipeline Company, halting operations. As a result, Colonial Pipeline eventually paid a ransom with support from the FBI. Colonial paid 75 bitcoin to the criminals (roughly USD 4.4 million, although 63.7 of the bitcoins have since been recovered).
For every ransomware attack that makes the news, there are many, many more that do not. But what is ransomware exactly? Allow us to explain.
What is Ransomware?
Ransomware is a form of malware. It seizes access to a user’s digital data with the threat of publishing personal information online or permanently blocking access to it via encryption or deletion. In other words, it takes your files and threatens to upload them on the dark web or permanently blocks your access to them unless you pay up.
Victims are invited to pay a ransom to recover their files to avoid their information being released, hidden from their view or deleted. Once the fee is paid, victims receive a decryption key that, in theory, restores access to their files.
Payment is usually made in Bitcoin. Ransoms vary from hundreds of dollars to many millions, depending on the data captured, the organization in question etc.

Anyone who holds critical data in a digital space could fall victim to ransomware. However, tempting targets for criminals tend to include universities, financial institutions, law firms, medical organizations and government agencies. One of the more common ransomware delivery systems is phishing, which is why a security awareness training program, ideally paired with phishing testing exercises, is so important. Yet, there are many delivery paths.
The absolute best way to avoid falling victim to ransomware is to keep it out in the first place. In other words, have robust data security practices, support and infrastructure in place. Ensure you’re following good data hygiene and performing regular backups that are securely stored separately from the rest of your infrastructure so that the backups are not also vulnerable to ransomware (backups are always cheaper than paying ransoms). SeekingFire Consulting Inc. can help with all of this!
However, even if you do all the right things, ransomware may still find a way in. The risk is never 0%. Doing the right things can reduce it but not eliminate it. With that in mind, this article is based on whether you should pay the ransomware ransom or not. So, for a moment, let’s pretend you’ve fallen victim to an attack.
To pay or not to pay?
It’s a question many people around the globe have wrestled with. Cybercriminals, while undoubtedly being malicious actors, are often sophisticated and intelligent. Their ransom requests are usually relatively in line with the data that they have access to. In other words, they set their price accordingly and are prepared to negotiate.
Whether you should pay or shouldn’t pay is probably not a one size fits all answer. Some may refuse to pay on principle or refuse to pay as they don’t want to encourage more cybercrime. As a general rule, that’s hard to disagree with.
However, others still may look at the $1,500 ransom and consider it a ‘cost of doing business.’ Some are even building ransomware demands into their annual budgets. Although, that money may be better spent on more robust security measures and training in the first place, especially as the ransom line item in the budget typically doesn’t take into account the business outage impact on revenues and the potential impact on brand reputation.
Ultimately, the decision will depend on the information lost as well as the ransom demanded, your insurance situation and what you can afford to risk. With that said, even paying up is not a guarantee you’ll get all of your data back.
The Sophos State of Ransomware 2021 Report details that 32% of organizations who fell victim to ransomware decided the best course of action was to pay up. But, dealing with criminals is not an exact science. Only 8% of those who agreed to pay got all their data back. Put another way, out of those that pay up, 92% never get all their data back. Sophos also revealed that recovery (rebuilding etc.) from a ransomware attack typically costs ten times the average ransom. With that in mind, it’s understandable that some organizations roll the dice and pay the ransom. But, again, regular backups are your friend!

If you’re the victim of a ransomware attack, contact a cybersecurity professional who can help you assess the scale of the problem. From there, you can work together to determine the most sensible next steps. Better still, have a trusted cybersecurity professional that you already work with who you can call in at a moment’s notice (we can fill this role for you—for a $0 ongoing retainer too!)
Of course, you may also want to contact the appropriate authorities and perhaps seek legal advice—after all, we’re data security professionals, not lawyers or police officers!
The ideal strategy is to limit your ransomware risk exposure in the first place. However, if disaster still strikes, stay calm, contact a trusted cybersecurity professional and see what you’re working with.
At SeekingFire Consulting, we’ve made the digital world a safer, more secure place since 2005. Based in Kelowna, BC, and serving clients across Western Canada, we offer a no-judgement, free consultation to all prospective clients. If you would like to discuss your data security needs, please reach out.
Disclaimer
While we have made every effort to present accurate, unbiased and helpful information in this article, please note that it reflects the author’s opinion and is written for the purposes of general knowledge, information and discussion. This article is not intended as legal advice, nor should it be considered as advice specific to your individual data security situation. If you would like to discuss your cybersecurity needs in specific detail, please get in touch with us.




